A snippet of the contents :
---------------------------------------------------------------
Table of Contents
- 1. Foreword
- 2. Prerequisite
- 2.1. PCI BUS
- 2.2. ISA BUS
- 3. Some Hardware Peculiarities
- 3.1. BIOS Chip Addressing
- 3.2. Obscure Hardware Port
- 3.3. "Relocatable" Hardware Port
- 3.4. Expansion ROM Handling
- 4. Some Software Peculiarities
- 4.1. Call Instruction Peculiarity
- 4.2. Retn Instruction Peculiarity
- 5. Our Tools of Trade
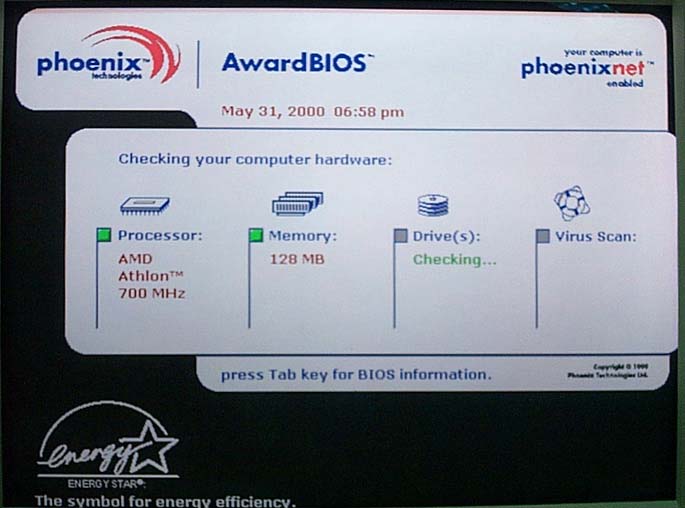
- 6. Award BIOS File Structure
- 6.1. The Compressed Components
- 6.2. The Pure Binary Components
- 6.3. The Memory Map In The Real System (Mainboard)
- 7. Disassembling the BIOS
- 7.1. Bootblock
- 7.1.1 "Virtual Shutdown" routine
- 7.1.2 Chipset_Reg_Early_Init routine
- 7.1.3 Init_Interrupt_n_PwrMgmt routine
- 7.1.4 Call To "Early Silicon Support" Routine
- 7.1.5 Bootblock Is Copied And Executed In RAM
- 7.1.6 Call to bios decompression routine and the jump into decompressed system bios
- 7.2. System BIOS a.k.a Original.tmp
- 7.2.1. Entry point from "Bootblock in RAM"
- 7.2.2. The awardext.rom and Extension BIOS Components (lower 128KB bios-code) Relocation Routine
- 7.2.3. Call to the POST routine a.k.a "POST jump table execution"
- 7.2.4. The "segment vector" Routines
- 7.2.5. "chksum_ROM" Procedure
- 7.2.6. Original.tmp decompression routine for the "Extension_BIOS components"
- 7.1. Bootblock
- 8. Closing
I'm looking forward your feedback